Technology has dramatically reshaped the average workplace all over the world in the last couple of decades and especially in online business security. The business environment of yesterday is slowly getting obsolete and has been taken over by rapid technological advancement, allowing employees to interact with a global market, and even take work out on the road or work from home.
The influx of new and modern technologies has been making the general convenience of business processes grow exponentially, and it’s safe to say it’s taken over the majority of our professional lives as well. Keeping a workplace up-to-date and profitable requires many technological implementations that we very often take for granted.
Many businesses have come to realize the necessity for innovation and technological advancements to keep up or be ahead of the competition but many businesses ‘do not’ realize that this is less than half the battle. Implementation is one, but improper security measures of technology and personal data could shatter your investments in technology and in a lot of cases, could be fatal to the business.
As businesses, our focus tends to be more towards profitability and operational costs, we tend to take a lot of our basic technology implementations for granted. What seems to be as harmless as your employee’s phones, USB devices, Email Client or Wifi could actually ruin the millions or billions of dollars your company is worth.
Seems a little far-fetched?
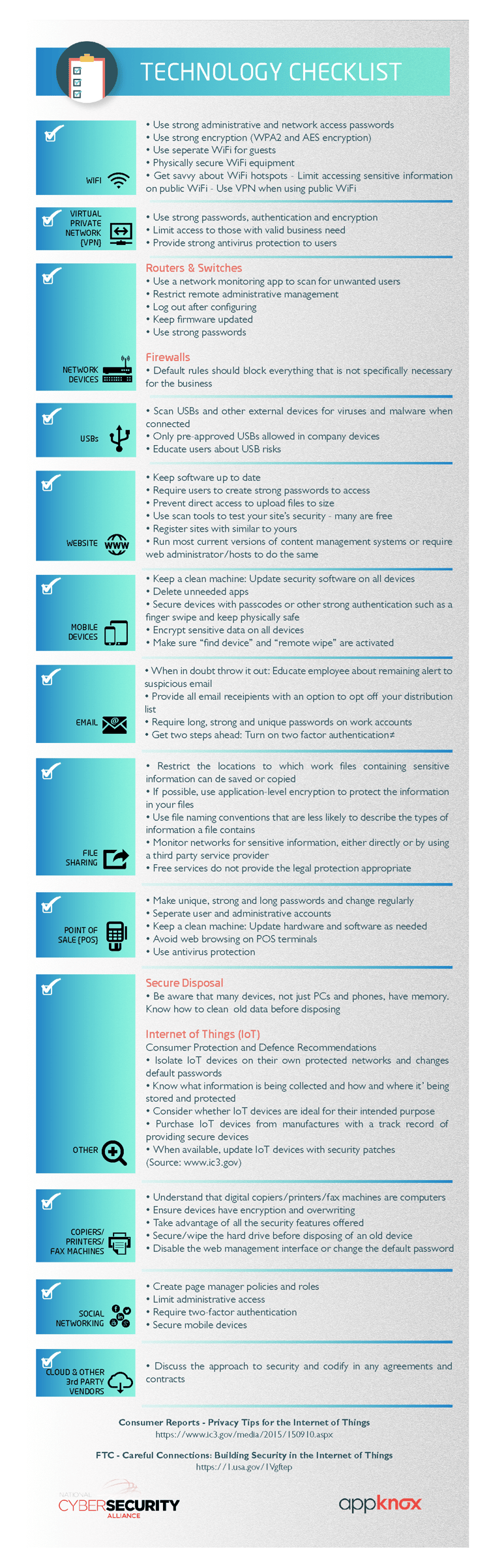
Target, Walmart, and eBay have all had their online business security compromised, and it’s usually due to some ridiculous errors with regards to technology implementation. Let’s not alarm you anymore than we already have. We’re here to help and here’s a list of the necessary technology checks for your online business security that you could go back and take a look at once again (if you haven’t already).
This checklist is designed to help you identify the technology in your business that you need to protect on priority. In addition, there are some basic security tips, considerations, and links to resources that can help you learn more to detect, respond and recover from any possible unforeseen cyber incidents.
Online Business Security: 13 technologies you may have, but must not ignore
We've talked about how important it is to protect consumer data before but protecting consumer data doesn't only mean hiring expensive agencies or resources to help with security. A lot of cyber crimes which happen stem from silly things we totally disregard. We've mentioned above the simple technologies that often are taken for granted, we hope you go back and incorporate this module as a part of your security checks. The effort is way lesser than when you will probably get hacked.


.jpg)
 Gartner and G2 recommends Appknox | See how we can help you with a free Demo!
Gartner and G2 recommends Appknox | See how we can help you with a free Demo!
 Darell Khin
Darell Khin










_HighPerformer_HighPerformer.png)
_BestEstimatedROI_Roi.png)

