Businesses have known for a long time that there always are weak links in security, especially mobile security. The worse part is not that businesses get affected by these security issues, but the fact that public awareness is terribly low on how vulnerable this can be. The man-in-the-middle attack has been one of the most exploited ways hackers have tried and managed to steal information and money.
What is Man in the Middle attack (MITM)?
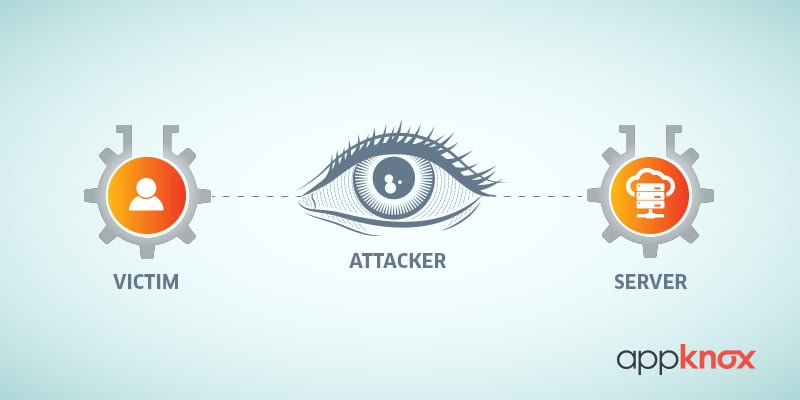
When an attacker secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other, it is called 'man in the middle attack. In simple words, a third person tries to break a connection between two people without them realizing this and is thus able to sniff and retrieve communication between them.
In fact, public WiFi networks have been the best playground for hackers to perform a man-in-the-middle attack. In recent times, there has been a steep increase in the frequency as well as the severity of such kinds of attacks.
In simple words, by listening in and intercepting a mobile device's traffic, hackers can get access to the data flowing to and from the mobile device and hence can gather sensitive information.
As mentioned before, the worse part of this is that public awareness about this is very low and hence when such things happen, the final effect is on enterprises and it can be terrible. If you are wondering how your business gets affected by this then listen to this.
If employees are careless about their information or data in public wifi networks on their personal devices, you can be sure it's the same happening on their work devices. This becomes scarier if their personal and work device is the same
Types of Man in the Middle Attack (MITM)
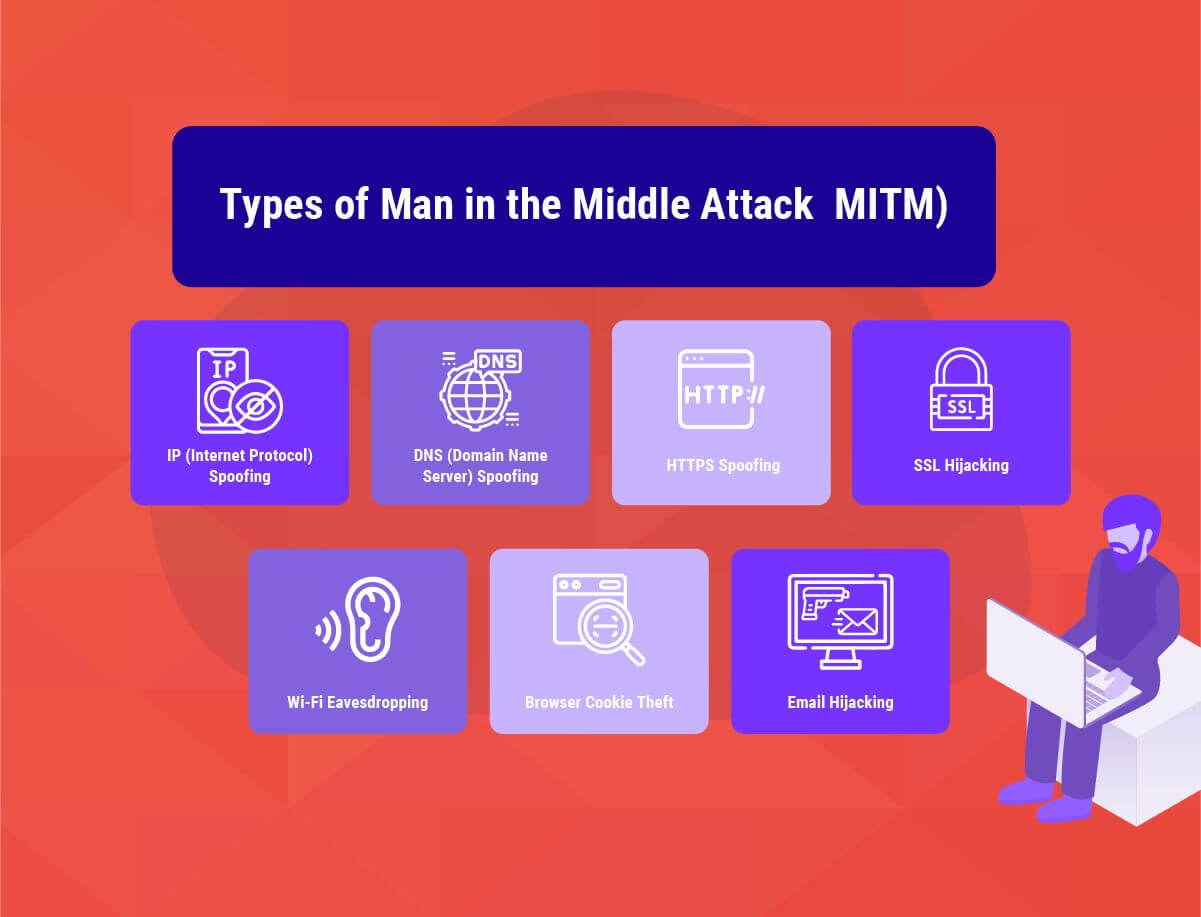
There are a variety of MITM attacks utilized by cybercriminals to gain control of sensitive networks and devices. The major types of MITM attacks include:
1. IP (Internet Protocol) Spoofing
Similar to the address of our homes, every device which can connect to the internet has an internet protocol address (IP address) assigned to it. Attackers spoof IP addresses and trick users into thinking that they are interacting with a genuine website or person over the internet (which they are not) and steal sensitive information which the user would not have shared otherwise.
2. DNS (Domain Name Server) Spoofing
In the case of DNS spoofing, users are forced to unknowingly use a fake website created by the attacker rather than the original one they were trying to visit. Victims of DNS spoofing may think that they are visiting a trusted and safe website when actually they are on a fake one and interacting with a threat actor. The goal of the man-in-the-middle here is to divert the traffic from the real website to the fake one and gain access to user login credentials.
3. HTTPS Spoofing
Seeing HTTPS in the URL is generally a very bold sign of security and trust. But this doesn't mean the attackers leave the stones unturned for HTTPS domains. In HTTPS spoofing attacks, the hackers use domains that look very similar to the original domain with a very slight difference in the non-ASCII characters. The users generally fall for this and are redirected to an insecure domain where all their interactions are monitored by the attackers.
4. SSL Hijacking
SSL or the Secure Sockets Layer is a security protocol that establishes secure and encrypted links between the web server and your browser. In the case of SSL hijacking, the attackers unencrypt the communication between the web server and client to be able to stage a MITM attack. In the process, the threat actors intercept all the secure information being communicated between the client (user's browser or application) and the server.
5. Email Hijacking
In many cases, the threat actors target the email accounts of organizations, especially financial institutions, and use that to target their customers. The attackers then send their own instructions to the customers by spoofing the email addresses of the organization. The users are convinced to follow the instructions sent by the attackers and unwillingly share sensitive financial information and even end up doing fraudulent transactions.
6. Wi-Fi Eavesdropping
Cybercriminals generally set up fake Wi-Fi connections which sound familiar to the users, sometimes similar to the names of their home Wi-Fi or a nearby business. Once the users onboard such Wi-Fi connections, the attackers are able to track the online activity of the users and gain access to their personal login info, payment-related information, and much more. In most cases, these Wi-Fi connections are public and require no authentication from the users.
7. Browser Cookie Theft
Websites store a small piece of information about your online activity on your computer in the form of browser cookies. For example, an e-commerce website might store some information related to your past purchase or your cart additions and login information so that you don't have to re-enter that information once you visit their website again. In several cases, these cookies are hijacked by attackers to gain access to your passwords, addresses, and other sensitive data.
How Safe is Your Data?
The data which is in transit and travels across your mobile device and servers goes to places beyond your imagination. So, is it safe and can we be sure that nobody can sniff into the sensitive personal information that we share with a number of apps and services we use?
The data generated from our mobile devices is transmitted over the WiFi network or the mobile connection to the base transceiver station (also known as BTS) of the operator. Then the data is redirected several times to a number of receiving stations.
During its journey, the data is assessed by several automated agents like antivirus and antispam appliances. And on every such instance, when the data is even under someone's supervision, it is possible that someone could illegally eavesdrop on it and access information you would never wish to share with someone.
Related topic- 11 Mobile Application Security Facts You Need to Know
MITM Attack On Mobile Applications
The man in the middle attack is not something new. They have been around for a few years now but have been mostly restricted to computers and laptops. With mobile growing at a fast pace, there has been a shift in emphasis to hacking mobile devices. This is particularly worrying as this gives access to a lot of information like personal identity, location, and messages. In fact, hackers can also eavesdrop on conversations.
Mobile apps need to communicate with remote servers in order to function, and most use HTTPS to do so securely. Problems arise however when apps fail to use standard authentication methods properly. Some, for example, don’t reliably check the certificate that proves a server is what it says it is. Others fail to properly verify their server’s hostname.
To be secure, mobile apps have to validate the hostname, ensure the certificate matches the server’s hostname, and ensure the certificate is trusted by a valid root authority.
How does MITM Attacks Happen?
Almost all MITM attacks happen with a straightforward order of execution, despite the variety of techniques used for the attack. These attacks can generally be divided into three operational stages. In the first stage, the attacker obtains access to the location from which he can execute the attack.
In the next stage, the attacker actually becomes the man in the middle by intercepting the peer-to-peer communication, and in the final stage, he overcomes any existing encryption to steal information.
The MITM attackers sit between the established connection of two parties in order to manipulate or just observe the ongoing traffic. This can be done either by manipulating existing legitimate networks or creating completely fake replicas of the network with the attackers themselves in control. Then they dismantle any kind of encryption that is there on the compromised traffic and change or reroute it to a destination of their own choice.
In many cases, the attackers silently keep on re-encrypting the compromised traffic to its target or just merely observing it. This makes MITM a very difficult attack to identify.
Are MITM Attacks that Easy to Execute?
A common perception is that MITM attacks are fairly easy to execute. As WiFi traffic is generally broadcasted out in the open, any device nearby can sniff on your data traffic.
If someone is using an unencrypted or public WiFi and connecting to some web page via HTTP, the job becomes even easier. Attackers commonly use technologies like Aircrack-ng and WiFi pineapples to lure users into their open WiFi networks and perform a MITM attack easily.
In fact, there are hundreds of automated tools and online tutorials available on the internet, especially on YouTube, which make it sound like anyone could easily do it.
Who is at risk of such attacks?
Simply put, everyone in the mobile enterprise is a potential target, but the most vulnerable are those in senior or executive positions in business and government. It is obvious that hackers look out for people who are important or have access to sensitive information.
Although, nowadays, since most businesses have started allowing employees to use their personal devices at work, this threat now impacts everyone almost equally. More often than not, it is easier to get access to a network through a device that you would think has the least probability of getting hacked.
The problem is very real and serious. More than 75% of the apps on the Google Play store do not meet basic security checks. Before you start thinking that you are safe on iOS, let me tell you that iOS is equally prone to such attacks.
How to Prevent MITM Attacks?
Preventing MITM attacks requires several small but practical steps on the part of users and a combination of verification and encryption methods on the part of the application and web developers.
Users can play their part by avoiding connecting to Wi-Fi networks that are not password protected. Users should strictly avoid using public networks while doing sensitive transactions like bank transfers or logins. Paying close attention to the notifications sent by your browser when it flags some websites as unsecured and logging out of applications when they are not in use can also go a long way.
For developers, it becomes essential to implement secure communication protocols like HTTPS and TLS which help mitigate hijacking and spoofing attacks by authenticating and encrypting the data in transit. This practice prevents the decryption of sensitive data like authentication tokens and also avoids the interception of site traffic.
It is also advisable for the application developers to use SSL/TLS and strengthen the security of each and every page rather than just focusing on the pages that require login credentials from the users. This massively reduces the chances of a hacker stealing session cookies when a user is browsing an unprotected section of the website or the application while logged in.
Conclusion
Man-in-the-middle attacks ( MITM ) pose a very serious threat when it comes to the web app or mobile application security. If protection measures are not in place, these attacks are easy to execute and difficult to detect and reward the attackers with access to a plethora of sensitive user and business-related information.
Given the level of damage, these attacks can do, it becomes critical for business stakeholders to understand and identify their underlying vulnerabilities and implement all the preventive measures to keep their infrastructure safe and secure from these attacks.




.jpg)
 Gartner and G2 recommends Appknox | See how we can help you with a free Demo!
Gartner and G2 recommends Appknox | See how we can help you with a free Demo!
 Harshit Agarwal
Harshit Agarwal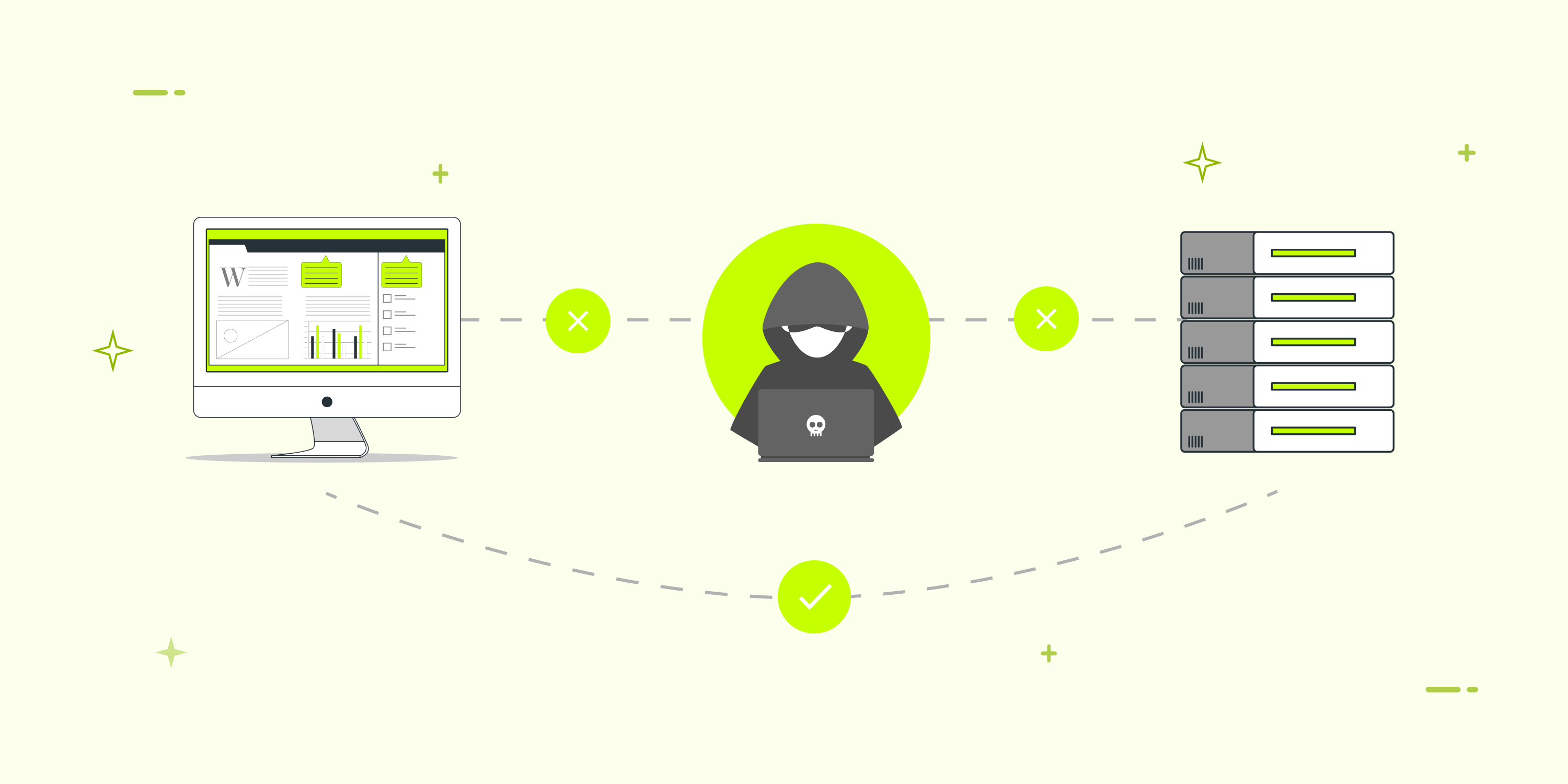










_HighPerformer_HighPerformer.png)
_BestEstimatedROI_Roi.png)

