Vulnerability Assessment and Penetration Testing is an everyday thing at the Appknox office. On a daily basis, apart from helping our customers stay safe, we also spend a lot of time testing new apps for security loopholes. Sometimes these tests can end up being really exciting, yet scary! Like the Ola Cabs hack that we did last year where we showed how someone could exploit a logical issue and make money out of thin air.
One such day, it was lunch time, and our security research team decided to test our favorite food ordering app. What they discovered was very exciting for them and equally scary for me as a business owner. Our whitehat security hackers found a checksum issue which means that we could order food of a higher value by paying much less. What this means is, as a user, you can order food for say Rs 500 but actually, pay only Rs 10 for it. This is a pretty severe issue for the business as it can result in a direct revenue loss.
Related post- The Importance of Checksum and How we Got Free Food Part 1
How We Managed to Get Free Food
Typically security problems are weaknesses in an application that result from a broken or missing security control - authentication, access control, input validation, etc. In contrast, business logic related vulnerabilities are ways of using the legitimate processing flow of the application in such a way that it results in a negative consequence to the business. Often this cannot be tested using automated methods and thus involves manual penetration testing.
So, here's what we did:
1. Add some item to cart
2. Intercept the traffic of the app using a tool like Burp Proxy
3. When you click on "Cart" in the app, you'll see the original requests going on in the proxy with an order amount of, say Rs. 274.8
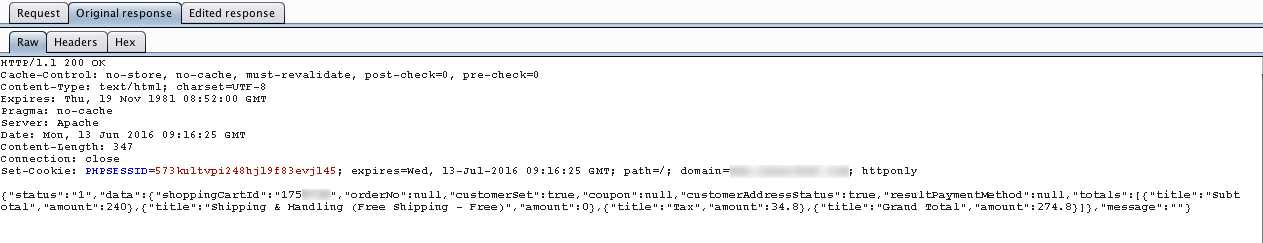 4. Now tamper the amount to Rs. 20.8 or any amount of your choice as shown in the screenshot below:
4. Now tamper the amount to Rs. 20.8 or any amount of your choice as shown in the screenshot below: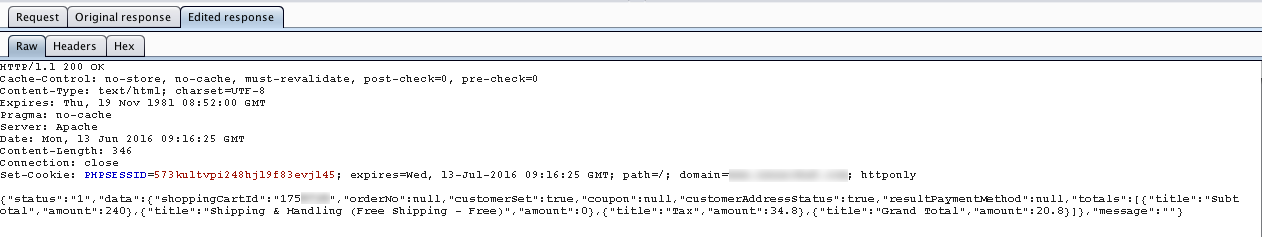
5. Now Paytm will ask you to pay Rs. 20.8 as shown in the screenshot below :
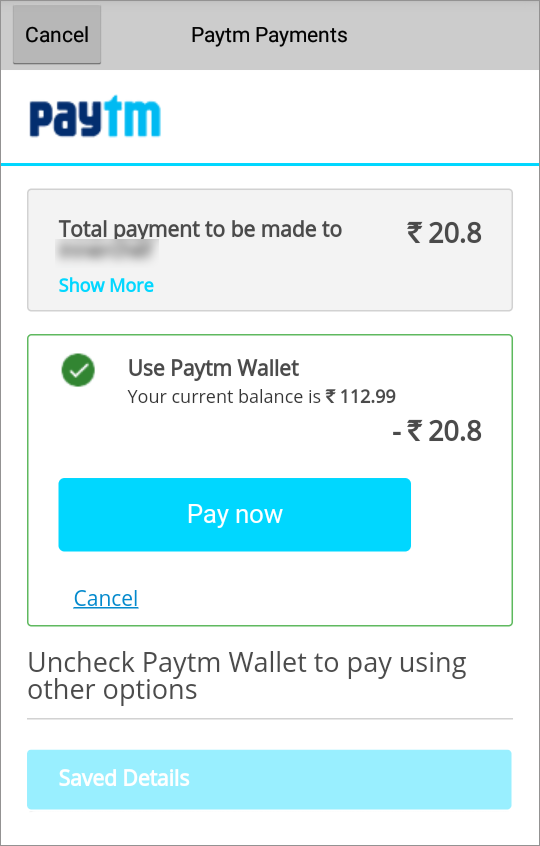
6. Once the payment was done, the order will be placed and you will receive the order number as shown in the screenshot below:
The Business Impact
As you can see, the app still thinks that we paid the full amount and the order as been confirmed. This is a simple process that anyone with basic technical knowledge can achieve. A vulnerability like this can hit the business hard if people start exploiting it. We made a disclosure about this issue to the business in concern around two months back, and they were thankful that this was brought up.
Not many companies respond back with a similar attitude. We've had situations where companies say they are aware of the issue and have too many things to take care at the moment. As a consumer, this troubles me a lot because it shows the lax attitude of businesses. And issues like these are not very difficult to fix.
The above-mentioned vulnerability can actually be possible in many different situations:
Example 1: Suppose an e-commerce app allows users to select items for purchase, view a summary page and then tender the sale. Consider a situation where an attacker is able to go back to the summary page, maintaining the same valid session, and inject a lower cost of all these items and then checkout.
Example 2: What if a user makes a transaction that allows points to be added to their loyalty card and then cancels the transaction after the points have been added. Will the points still be valid for that account?
Well, at the end of the day, as a business owner or CXO, it is essential that you at least know and understand the threats to your business assets. Whether you decide to take action on it or not is the second stage of addressing the problem. We always ask our customers to stay informed and proactive, especially because security is something that needs to be taken care of every single day.
If you want us to run a quick analysis of your app and let you know what we find, we'd be happy to do that (no charge!).




 Gartner and G2 recommends Appknox | See how we can help you with a free Demo!
Gartner and G2 recommends Appknox | See how we can help you with a free Demo!
 Subho Halder
Subho Halder










_HighPerformer_HighPerformer.png)
_BestEstimatedROI_Roi.png)

